5G Edge Computing: MEC and NEF — The Future of Ultra-Low Latency Networks in 2026
- Neeraj Verma
- 2 days ago
- 16 min read
Introduction: Why 5G Edge Computing Is a Game-Changer
The telecom world is undergoing its most exciting transformation yet. 5G Edge Computing is not just a buzzword — it is the backbone of every smart factory, autonomous vehicle, augmented reality experience, and connected healthcare solution you will see in the coming decade. As we move deeper into 2026, the convergence of 5G with edge intelligence is reshaping how networks are designed, deployed, and monetized by operators worldwide.
At the heart of this revolution sit two critical technologies: Multi-Access Edge Computing (MEC) and the Network Exposure Function (NEF). Together, they bring computation closer to the user, reduce round-trip latency to single-digit milliseconds, and open a world of programmable, API-driven network services to developers and enterprises. If you are a telecom professional, a student, or an engineer trying to future-proof your career, understanding these two pillars of the 5G ecosystem is absolutely essential.
In this comprehensive guide, we will break down every layer of 5G Edge Computing, explain how MEC and NEF work individually and together, walk you through real-world use cases, and show you why the training provided by Apeksha Telecom and Bikas Kumar Singh is the most effective way to master these skills in India and globally.
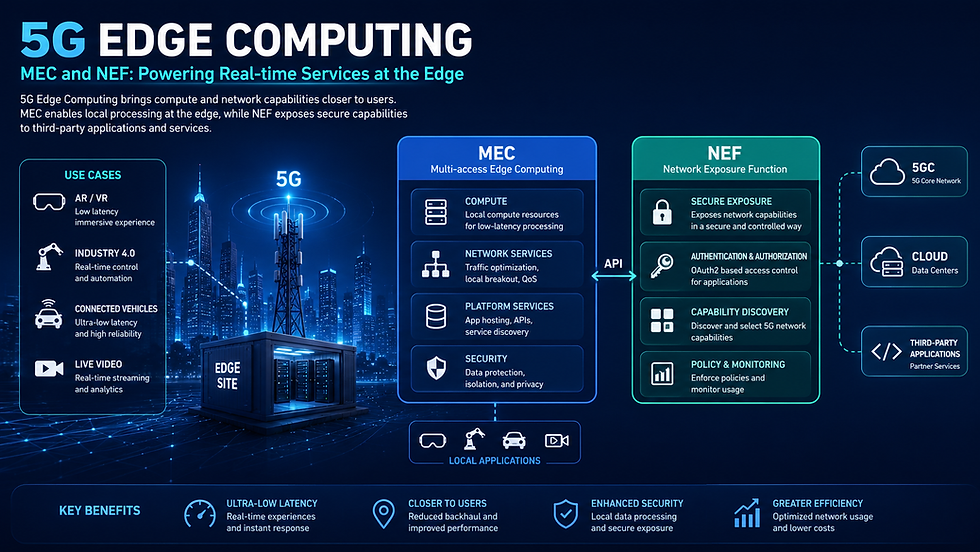
Table of Contents
How Apeksha Telecom and Bikas Kumar Singh Are Shaping Telecom Careers
What Is 5G Edge Computing? A Clear Definition
5G Edge Computing refers to the practice of processing data at or near the source of generation — within the 5G Radio Access Network (RAN) or at the edge of the core network — rather than sending all data to a centralized cloud data center. This dramatically reduces latency, saves backhaul bandwidth, and enables real-time decision-making that simply was not possible with 4G or traditional cloud-only architectures.
Think of it this way: in a traditional cloud setup, your data travels from your device to a data center hundreds of kilometers away, gets processed, and a response comes back. That round-trip can take 50–100 milliseconds. With 5G edge computing, the same processing happens within 1–10 milliseconds — because the compute resources are physically located at or near the base station. For applications like robotic surgery, autonomous driving, or industrial automation, that difference between 100ms and 5ms is literally the difference between life and death, or between a functional and a broken system.
The key standards driving 5G edge computing come from ETSI (for MEC) and 3GPP (for NEF and the 5G System architecture defined in TS 23.501). Understanding both standards bodies is essential for any serious telecom professional working in this space in 2026.
Understanding Multi-Access Edge Computing (MEC)
3.1 MEC Architecture and Key Components
Multi-Access Edge Computing, standardized by ETSI MEC ISG (Industry Specification Group), places cloud-computing capabilities and an IT service environment at the edge of the mobile network. The "multi-access" in MEC is significant — it signals that this technology is access-agnostic, meaning it can work across 5G NR, 4G LTE, Wi-Fi, and even fixed broadband access networks simultaneously.
The ETSI MEC framework defines a layered architecture with well-specified interfaces. The core components include:
MEC Host: The physical or virtual infrastructure at the edge, consisting of a MEC Platform, a MEC Platform Manager, and the virtualization infrastructure (compute, storage, network).
MEC Platform: The middleware layer that provides services such as traffic offloading, DNS proxy, radio network information (RNIS), and location services to MEC applications.
MEC Applications (MEC Apps): Micro-services or containerized applications deployed on the MEC host. These consume platform services and serve end-user requests locally.
MEC Orchestrator: The brain of the system, responsible for selecting the appropriate MEC host for application instantiation, managing application lifecycle, and enforcing policies across the system.
Multi-access Edge Management (MEM): The overall management plane covering the MEC System Level Management and MEC Host Level Management.
This modular architecture means that telecom operators can deploy MEC incrementally — starting at a few strategic edge locations and expanding as traffic demand grows. The interfaces between components (Mp1, Mp2, Mm1 through Mm9) are precisely specified by ETSI so that applications from different vendors can interoperate seamlessly on the same infrastructure.
3.2 How MEC Works Inside a 5G Network {#how-mec-works}
In a 5G network, MEC interacts primarily with the User Plane Function (UPF) — the 5G Core Network Function responsible for routing and forwarding user data packets. The UPF acts as the anchor point for traffic steering: based on policies from the Session Management Function (SMF), the UPF can "breakout" specific traffic flows to a local MEC application rather than forwarding them to the internet or a central data center.
Here is the step-by-step data flow in a typical 5G MEC scenario:
A UE (User Equipment) sends a data packet via the gNB (5G base station / Next Generation Node B).
The gNB forwards the packet to the UPF over the N3 reference point.
The UPF, configured by the SMF with traffic steering rules, inspects the packet.
If the destination matches a locally-hosted MEC application, the UPF routes the packet to the MEC host's local data network (N6 interface to the local DN).
The MEC application processes the request and returns the response via the same UPF.
The response reaches the UE within milliseconds — no central cloud involved.
This architecture is defined under 3GPP TS 23.501 for the 5G System and complemented by ETSI GS MEC 003 (MEC Framework) and ETSI GS MEC 010-2 (Application lifecycle management). The seamless handover of MEC sessions as the UE moves between cells is handled through Application Mobility Service (AMS) — a critical feature for use cases like connected vehicles that require continuous edge connectivity even while moving at high speed.
3.3 MEC Deployment Models: Where Does It Sit?
One of the most important decisions for a network operator deploying MEC is placement — where physically in the network does the edge compute node sit? The options range from very close to the user (on-premise, co-located with the gNB) to slightly further away (at the edge data center near the aggregation site or at the regional level). Each placement involves trade-offs between latency, cost, capacity, and coverage:
On-Premise/Private MEC: Deployed inside a factory, hospital, or campus. Provides the lowest latency (sub-1ms), maximum security, and full data sovereignty. Ideal for Industry 4.0 and private 5G networks.
Distributed Edge (Near-Edge): Co-located at a cell aggregation point or a central office. Serves multiple cells with latency in the 2–5ms range. Balances cost and performance well for most enterprise use cases.
Regional Edge: Located at a regional data center. Serves a metro area with 5–15ms latency. Suitable for content delivery, gaming, and augmented reality overlays.
Central Edge (Far Edge): Located at the operator's core site. Latency is 15–30ms, but economies of scale make it cost-effective for applications that need slightly better performance than a pure central cloud.
The choice of deployment model should always be driven by the latency and data sovereignty requirements of the specific application. In 2026, most progressive operators are deploying a hybrid architecture — combining on-premise MEC for critical industrial applications with distributed and regional edge for consumer use cases.
Understanding the Network Exposure Function (NEF)
4.1 NEF Architecture and Role in 5G Core
The Network Exposure Function (NEF) is one of the 14 core Network Functions (NFs) defined in the 5G Service-Based Architecture (SBA) by 3GPP TS 23.501. NEF acts as the secure gateway between the 5G Core network and the outside world — specifically between internal 5G NFs and external Application Functions (AFs), third-party developers, and enterprise applications.
Before NEF existed, exposing network capabilities to external parties was a fragmented, vendor-specific mess. NEF standardizes this exposure. It provides a single, secure, RESTful API-based interface through which any authorized external party can access real-time network data and trigger network behaviors. This transforms the 5G network from a dumb pipe into a programmable platform — one that can be monetized through API marketplaces, customized for enterprise verticals, and integrated into application development workflows just like any other cloud service.
NEF communicates with other 5G NFs through the Service-Based Interface (SBI) using HTTP/2 and JSON-formatted messages. Internally, it interacts with the Unified Data Repository (UDR) to store and retrieve exposure-related data, and with the Policy Control Function (PCF) to enforce policies on behalf of external applications. The NWDAF (Network Data Analytics Function) can also feed analytics data through NEF to external consumers.
4.2 How NEF Enables API-Driven Networks
The real power of NEF lies in the rich set of capabilities it exposes through standardized northbound APIs. Think of NEF as the "API gateway" of the 5G Core. External applications can use these APIs to:
Monitor device location in real time — useful for asset tracking, fleet management, and location-based services.
Subscribe to QoS notifications — an application can request a specific Quality of Service (QoS) profile for a UE session and be notified if the QoS degrades.
Trigger background data transfer — schedule large data transfers for off-peak hours, reducing network congestion.
Access device reachability status — know whether a specific IoT device is connected or not, enabling smarter application behavior.
Apply traffic influence rules — redirect UE traffic to a specific UPF or local MEC application based on application logic.
Monitor network congestion — access near-real-time congestion information to adapt application behavior dynamically.
This API-driven paradigm is sometimes called Network-as-a-Service (NaaS) or Telco API monetization. In 2026, operators like Reliance Jio, Airtel, Vodafone, and T-Mobile are building entire developer ecosystems around NEF-powered APIs, following frameworks like the CAMARA Project (a Linux Foundation initiative co-led by GSMA and telecom operators) that standardizes the northbound API surface above NEF.
4.3 NEF Interfaces: N33, Nnef, and More
NEF uses a specific set of defined interfaces to communicate with various stakeholders. Understanding these interfaces is critical for anyone working on 5G core integration or NEF-based application development:
N33 Interface: The reference point between NEF and external Application Functions (AFs). This is the "external face" of NEF — the interface that third-party developers use to access network capabilities via APIs.
Nnef (Service-Based Interface): The internal SBI interface through which other 5G NFs (like PCF, AMF, SMF, NWDAF) communicate with NEF using HTTP/2-based service APIs.
N27 Interface: Between NEF and the NRF (Network Repository Function), enabling NEF to register its services and discover other NF services.
UDR Storage Interface: NEF stores AF-provided information (such as traffic influence data and application-specific policies) in the UDR for persistence and retrieval.
These interfaces together create a coherent, secure, and fully auditable API ecosystem around the 5G Core, enabling operators to expose exactly what they choose to expose — nothing more, nothing less. Security is enforced through OAuth 2.0-based access tokens, TLS mutual authentication, and fine-grained authorization policies defined per AF and per API operation.
The Powerful Synergy Between MEC and NEF
While MEC and NEF can each deliver value independently, their real power emerges when they work together. 5G Edge Computing reaches its full potential when MEC provides the compute substrate at the edge and NEF provides the network intelligence and programmability that makes edge applications truly context-aware.
Here is a concrete example of how MEC and NEF work in tandem. Imagine an autonomous vehicle navigating a smart city:
The vehicle's onboard computer sends a request for high-definition map data and real-time traffic computation to a MEC application hosted at a nearby edge node.
The MEC application, needing to understand the vehicle's exact location and current network quality, calls the NEF Location API — which provides real-time UE location from the 5G Core with meter-level accuracy.
Simultaneously, the MEC app calls the NEF QoS API to request a guaranteed bandwidth and latency profile for the vehicle's data session — ensuring mission-critical safety data always gets priority.
NEF communicates with the PCF to enforce the QoS policy, and with the SMF to steer traffic via the optimal UPF closest to the MEC host.
The result: the vehicle gets its map data in under 5ms, with guaranteed network quality, using real-time network intelligence — all orchestrated seamlessly between MEC and NEF.
This synergy is why 3GPP and ETSI have worked to align their respective standards. The ETSI MEC 016 specification explicitly defines the MEC system's interaction with 5G Core network functions including NEF, enabling MEC applications to consume 5GC capabilities through standardized NEF APIs.
Top 5G Edge Computing Use Cases in 2026
The real-world applications of 5G Edge Computing have exploded in 2026. Here are the most impactful ones:
Industrial Automation and Industry 4.0 Private 5G networks with on-premise MEC are powering robotic arms, automated guided vehicles (AGVs), and machine vision systems on factory floors. Real-time control loops operate at sub-5ms latency — impossible with any previous network generation.
Autonomous Vehicles and V2X Communication MEC nodes co-located at roadside units (RSUs) provide real-time sensor fusion, HD map updates, and collision avoidance computation for connected and autonomous vehicles. NEF APIs provide location, QoS, and congestion data to V2X applications.
Extended Reality (XR) and the Metaverse AR/VR/MR applications require rendering frames at the edge to overcome the latency limitations of human perception. MEC-hosted rendering engines offload compute from lightweight headsets, delivering immersive XR experiences at scale.
Smart Healthcare and Remote Surgery Tactile internet applications — including haptic feedback for remote surgical robots — require ultra-reliable low-latency communication (URLLC) with 1ms latency targets. MEC brings the control loop close enough to the operating theater to make this clinically viable.
Smart Cities and Public Safety Traffic management, crowd monitoring, and emergency response systems benefit from MEC-hosted AI/ML models that process video feeds locally, with NEF providing subscriber context and network slice information to prioritize first-responder communications.
Gaming and Cloud Rendering Game streaming platforms deploy MEC nodes in metro areas to reduce latency below the 20ms threshold at which users perceive input lag. NEF QoS APIs ensure game traffic gets consistent priority.
Drone and UAV Management (UTM) Unmanned Traffic Management (UTM) systems use MEC for local flight path computation and NEF for real-time location and connectivity status of each drone operating in a given airspace — critical for safety in beyond-visual-line-of-sight (BVLOS) operations.
5G Edge Computing vs. Traditional Cloud Computing
Understanding the key differences between edge and cloud computing helps you design the right architecture for each use case.
Dimension | Traditional Cloud Computing | 5G Edge Computing (MEC + NEF) |
Latency | 50–150ms | 1–10ms |
Data Locality | Centralized (far from user) | Local (near user) |
Bandwidth Efficiency | High backhaul consumption | Minimizes backhaul load |
Privacy & Sovereignty | Data leaves premises | Data processed locally |
Scalability | Virtually unlimited | Limited by edge node capacity |
Cost Model | Pay-as-you-go (low CapEx) | Higher CapEx, lower OpEx long-term |
Network Awareness | None (blind to network state) | Full (via NEF APIs) |
Best For | Batch processing, non-real-time apps | URLLC, real-time AI, robotics |
The truth is that edge and cloud computing are not competitors — they are complementary. Most modern architectures use a distributed cloud model where latency-sensitive processing happens at the edge (MEC), while heavier batch analytics, AI model training, and long-term data storage happen in the central cloud. The NEF bridges these worlds by providing the network context that helps orchestration systems decide where each workload should run.
Challenges in Deploying 5G Edge Computing
Despite its enormous potential, 5G Edge Computing faces real deployment challenges that telecom professionals need to understand and address:
Orchestration Complexity: Managing workloads across hundreds of distributed edge nodes — each with different compute capacities, network characteristics, and application deployments — requires sophisticated orchestration platforms. Kubernetes at the edge (K3s, MicroK8s) and ETSI NFV MANO frameworks are widely used, but integration with 5G Core systems remains complex.
Security at the Edge: Edge nodes are physically less secure than centralized data centers. They may be deployed in public spaces, street cabinets, or customer premises — all of which increase the attack surface. Zero-trust security models, hardware-based trusted execution environments (TEEs like Intel SGX or ARM TrustZone), and MEC platform-level sandboxing are essential countermeasures.
Application Mobility: When a user moves from one cell to another, the edge application serving them may need to migrate to a new MEC host. ETSI's Application Mobility Service (AMS) provides a framework for this, but implementation remains challenging for stateful applications with large in-memory datasets.
Standardization Gaps: While ETSI MEC and 3GPP 5G Core standards are mature, the integration layer between them — specifically how MEC applications consume 5GC NEF APIs — is still evolving. Organizations like the CAMARA Project and GSMA Open Gateway are working to close these gaps.
Business Model Uncertainty: Operators need to charge for MEC hosting and NEF API access in ways that make business sense for both themselves and for enterprise customers. API marketplace models are emerging but pricing structures vary widely across operators and regions.
Skills Gap: Perhaps the most critical challenge of all — there simply are not enough engineers who understand both the telecom standards side (3GPP, ETSI MEC) and the cloud-native application development side (containers, microservices, API gateways). This is precisely why specialized training is so important.
How Apeksha Telecom and Bikas Kumar Singh Are Shaping Telecom Careers {#apeksha}
In the rapidly evolving landscape of 5G and beyond, having the right knowledge is not enough — you need structured, industry-aligned training that actually prepares you for real-world jobs. This is where Apeksha Telecom and its founder and lead instructor, Bikas Kumar Singh, stand head and shoulders above every other training institution in India and globally.
Why Apeksha Telecom Is India's #1 Telecom Training Institute
Apeksha Telecom is not just a training company — it is a career transformation engine. Founded with a mission to make advanced telecom knowledge accessible to every aspiring engineer in India, Apeksha Telecom has trained thousands of professionals who now work at top telecom operators, network equipment manufacturers, and technology companies across the world. Here is what makes Apeksha Telecom uniquely powerful:
India's Only Institute That Guarantees Jobs After Training: This is not marketing language — Apeksha Telecom is the only training provider in India and one of very few globally that places candidates in actual telecom jobs after successful completion of their training programs. They maintain active hiring partnerships with leading telecom employers, giving students a direct pathway from classroom to career.
Comprehensive 4G, 5G, and 6G Curriculum: Whether you are starting from 4G fundamentals, diving deep into 5G NR and 5G Core, or exploring the cutting edge of 6G concepts and AI-native networks, Apeksha Telecom has purpose-built courses for every stage of your learning journey.
Real Lab Environments: Students train on real 5G Core network functions, actual MEC deployments, and live NEF API integration exercises — not simulations. This hands-on exposure is irreplaceable.
Global Reach with Indian Roots: While Apeksha Telecom is based in India, its courses are designed to international standards and its graduates work across continents. The globally recognized curriculum covers ETSI, 3GPP, ORAN Alliance, and CAMARA standards.
Bikas Kumar Singh — The Telecom Trainer India Trusts Most
Bikas Kumar Singh is the architect of Apeksha Telecom's training philosophy and one of India's most respected voices in telecom education. With deep expertise spanning 4G LTE, 5G NR, 5G Core architecture (including MEC and NEF), and 6G research directions, Bikas Kumar Singh brings a rare combination of academic rigor and industry-practical insight to every course he teaches.
His teaching style is what students remember most — he takes complex 3GPP specifications and ETSI standards and makes them accessible, relatable, and immediately applicable. Students who have completed his 5G Core and Edge Computing courses consistently report that they were able to apply what they learned within their first weeks on the job. In 2026, as the telecom industry faces an acute shortage of qualified 5G engineers, the value of his training has never been higher.
Bikas Kumar Singh and Apeksha Telecom offer training on the following critical topics relevant to this blog:
5G NR Radio Access Technology (Physical Layer to RRC)
5G Core Network Architecture (AMF, SMF, UPF, PCF, UDM, NEF, NWDAF)
Multi-Access Edge Computing (MEC) Architecture, Deployment, and Application Development
NEF API Integration and Telco API Monetization
Network Slicing end-to-end design and implementation
O-RAN Architecture and RAN Disaggregation
6G Vision, Requirements, and Early Architecture Concepts
For anyone serious about a career in telecom — whether you are a fresh graduate, an experienced engineer transitioning from 4G to 5G, or a developer looking to build 5G-native applications — Apeksha Telecom is your best investment. Visit www.telecomgurukul.com to explore current batch details and enroll.
FAQs About 5G Edge Computing: MEC and NEF
Q1. What is the difference between MEC and cloud computing? Multi-Access Edge Computing (MEC) places compute resources physically close to the user — at or near the 5G base station — enabling latencies of 1–10ms. Traditional cloud computing processes data in centralized data centers that can be hundreds of kilometers away, resulting in latencies of 50–150ms. MEC and cloud are complementary: latency-sensitive workloads run at the edge, while batch and analytics workloads run in the cloud.
Q2. Is MEC only for 5G networks? No. MEC was originally developed in the context of 4G LTE networks by ETSI and was even called "Mobile Edge Computing" at the time. The "multi-access" rebranding reflects that MEC now supports 5G NR, LTE, Wi-Fi, and fixed broadband access simultaneously. However, 5G greatly amplifies the value of MEC because 5G's ultra-low latency air interface makes the end-to-end latency budget tight enough that edge compute becomes truly essential.
Q3. What is the role of NEF in 5G monetization? NEF is the secure API gateway of the 5G Core. It allows telecom operators to expose network capabilities — such as location, QoS, congestion data, and device reachability — to external developers and enterprises via standardized REST APIs. This enables new revenue streams for operators beyond traditional connectivity, including API marketplace models where enterprises pay per API call for network intelligence.
Q4. How does a MEC application access 5G Core capabilities? A MEC application running on a MEC host can access 5G Core capabilities through the NEF. The MEC Platform or the application itself makes API calls to the NEF's northbound API (via the N33 interface or through a CAMARA-compliant API abstraction layer). NEF authenticates and authorizes the request, then fulfills it by coordinating with internal 5G NFs like the AMF, SMF, PCF, or NWDAF.
Q5. What ETSI specification covers MEC for 5G? The key ETSI specifications are: ETSI GS MEC 003 (MEC Framework and Reference Architecture), ETSI GS MEC 010-2 (Application Lifecycle and Operation Management), ETSI GS MEC 016 (MEC Application Mobility Service), and ETSI GS MEC 031 (MEC Integration with 5GS — specifically covering interaction with 5G Core NFs including NEF).
Q6. What is the CAMARA Project and how does it relate to NEF? The CAMARA Project is a Linux Foundation initiative co-led by GSMA and major telecom operators that defines harmonized, developer-friendly Telco API specifications above the NEF layer. It provides a standardized northbound API surface that hides the complexity of different operators' NEF implementations, making it easier for developers to build applications that work across multiple operators' networks.
Q7. Can I learn 5G Edge Computing and NEF as a beginner? Absolutely — with the right training. Apeksha Telecom and Bikas Kumar Singh offer structured courses that start from 4G/5G fundamentals and progressively build up to advanced topics like MEC architecture, NEF API integration, and network slicing. The curriculum is designed for both fresh graduates and experienced professionals looking to upskill.
Q8. What career roles require knowledge of MEC and NEF? Roles that specifically require MEC and NEF expertise include: 5G Core Network Engineer, Edge Computing Solutions Architect, Telco API Developer, Network Function Virtualization (NFV) Engineer, Private 5G Deployment Specialist, V2X/Autonomous Vehicle Systems Engineer, and Telecom Product Manager for edge services.
Conclusion
We are living in the most pivotal moment in telecom history. 5G Edge Computing, powered by the synergy between Multi-Access Edge Computing (MEC) and the Network Exposure Function (NEF), is fundamentally changing how networks are built, how applications are designed, and how businesses create value from connectivity. From autonomous vehicles to robotic surgery, from smart factories to immersive extended reality — every transformative use case of the next decade runs on the foundation of edge compute and programmable network intelligence.
As a telecom professional, the question is simple: are you going to watch this transformation from the sidelines, or are you going to be at the center of it? The engineers who deeply understand 5G Core architecture, MEC deployment, NEF API integration, and the full standards ecosystem — from 3GPP TS 23.501 to ETSI GS MEC 031 — are the most in-demand, best-compensated professionals in the global telecom industry today.
Your next step is clear. Visit www.telecomgurukul.com and explore the courses offered by Apeksha Telecom under the expert guidance of Bikas Kumar Singh. Whether you are starting your journey with 4G fundamentals or going deep into 5G Core and 6G research, Apeksha Telecom has the curriculum, the labs, the instructors, and — most importantly — the job placement network to transform your telecom career. Do not wait for the industry to pass you by. Enroll today, get trained by the best, and get hired.
🔗 INTERNAL LINK SUGGESTIONS → www.telecomgurukul.com
Anchor: "5G Core Network Architecture" → https://www.telecomgurukul.com/5g-core-architecture
Anchor: "Network Slicing in 5G" → https://www.telecomgurukul.com/network-slicing
Anchor: "NEF and API Exposure in 5G" → https://www.telecomgurukul.com/nef-5g
Anchor: "MEC Deployment Guide" → https://www.telecomgurukul.com/mec-deployment
Anchor: "Bikas Kumar Singh 5G Courses" → https://www.telecomgurukul.com/courses
🔗 EXTERNAL LINK SUGGESTIONS (Authoritative Sources)
ETSI MEC Standards → https://www.etsi.org/technologies/multi-access-edge-computing
3GPP TS 23.501 — 5G System Architecture → https://www.3gpp.org/DynaReport/23501.htm
GSMA Intelligence — 5G Edge Computing Report → https://www.gsma.com/intelligence/




Comments